Thank you! Your submission has been received!
Close
Request a free consultation
We will help you find the right airspace security solution to protect against drone threats.

Airspace Security Specialist
at Dedrone
FOR Correctional facilties


The presence of a drone and any kind of disturbance resulting from that is a major threat not only to the safety of the staff that work in the facility but also to the offender population that live in the facility
Correctional facilities face a persistent, escalating threat: Contraband delivery by drones. The small unmanned aerial vehicles can easily bypass the most sophisticated security installations by simply flying over the top into a facility. After deploying the Dedrone solution, the opportunity for contraband delivery is greatly reduced.
107
Correctional Facilities
Rely on Dedrone

1
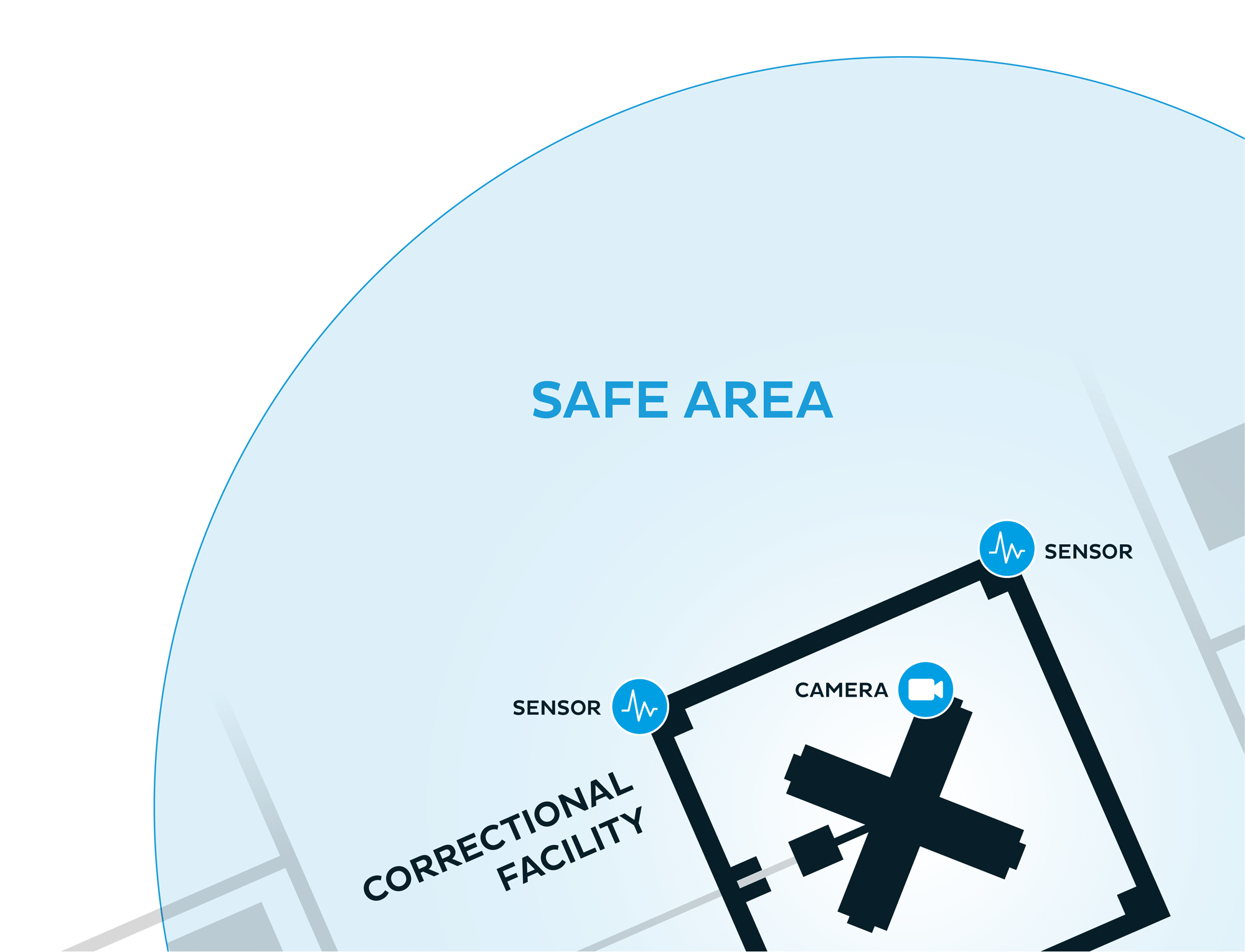
Define your airspace: Set up a customizable, pre-determined perimeter up to 5km (~80 km²) around the prison.

2
DedroneTracker.AI software detects, identifies, and locates drone threats. Dedrone gives early warning of drone-based threats, often before the drone takes off.
3
Based on Friend/Foe rules, DedroneTracker.AI automatically sends alerts to security teams when an unauthorized drone is detected.


4
By incorporating DedroneSensors and other sensors, such as a camera, users can track the flight path of the drone and determine the location of the pilot.
5
Dedrone not only locates the position of the drone, but also the pilot, enabling security teams to quickly mitigate the threat.


6
By documenting flight patterns, security teams can evaluate their current security measures for potential gaps like easy launch areas and update SOPs accordingly. Dedrone data can also be leveraged to provide evidence to share with law enforcement.
Detect, identify, track and analyze drone activity and their pilots with DedroneTracker.AI, a web-based solution that makes it easy to mitigate drone threats.